Smart alerting with AIOps
A trigger-based alerting in infrastructure management is currently insufficient to keep operations smooth and uninterrupted. AI-powered IT operations deliver smart alerts that not only improve a team’s ability to respond swiftly but can also deliver significant automation.
According to Gartner data quoted by the TechBeacon, 40% of organizations are predicted to strategically implement AIOps to enhance performance monitoring by 2022. The reason is obvious: AIOps helps build resilient and reliable IT corporate ecosystems. It also boosts overall company performance, an area that can always be improved. For example, for 34.4% of organizations it takes more than 30 minutes on average to resolve IT incidents impacting consumer-facing digital services.
The standard approach to alerting
In the traditional approach to automating IT operations, sets of previously defined conditions triggered alerts.
A huge drawback of this approach was that problems had to be identified, defined and researched. Rules were then set to react to the problem when it occurred. This approach was effective only in dealing with problems that had already come up, but it was useless when conditions changed. That’s common in IT infrastructure.
Also, manually setting the rules opens the process up to mistakes hidden within the code and rules – the more complicated the system or instruction, the better hidden a malfunction can be. And there it lurks, ready to hit right when the rule should have saved the infrastructure.
This is where AI tools come in handy.
How AIOps makes basic alerting smart alerting
The key difference between trigger-based alerts and AI-powered alerts is that the first comes with a huge amount of manual work, while the second can cut workloads significantly by automating the most tedious tasks (read more about that in our What is AIOps blog post).
Both types of alerts send a constant flow of data in from the system, including logs, events or metrics collected by sensors. However, only in the AI alerts is the data preprocessed and initially analyzed before a human gets it–stripped of the noise and chaos usually seen in the raw data.
Pattern recognition-based alerting
Unlike in less sophisticated systems, AI-powered solutions deliver pattern-based, rather than triggered, alerting. The core difference is in recognizing not a particular, single event or a chain of events that occur within the network, but the overall pattern of a malfunction or attack. Thus, if there is a new channel or technology used, the system will remain vigilant. Read more about that in our AIOps for Network Traffic Analysis (NTA) blog post.
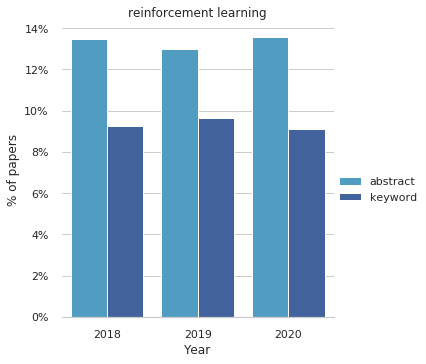
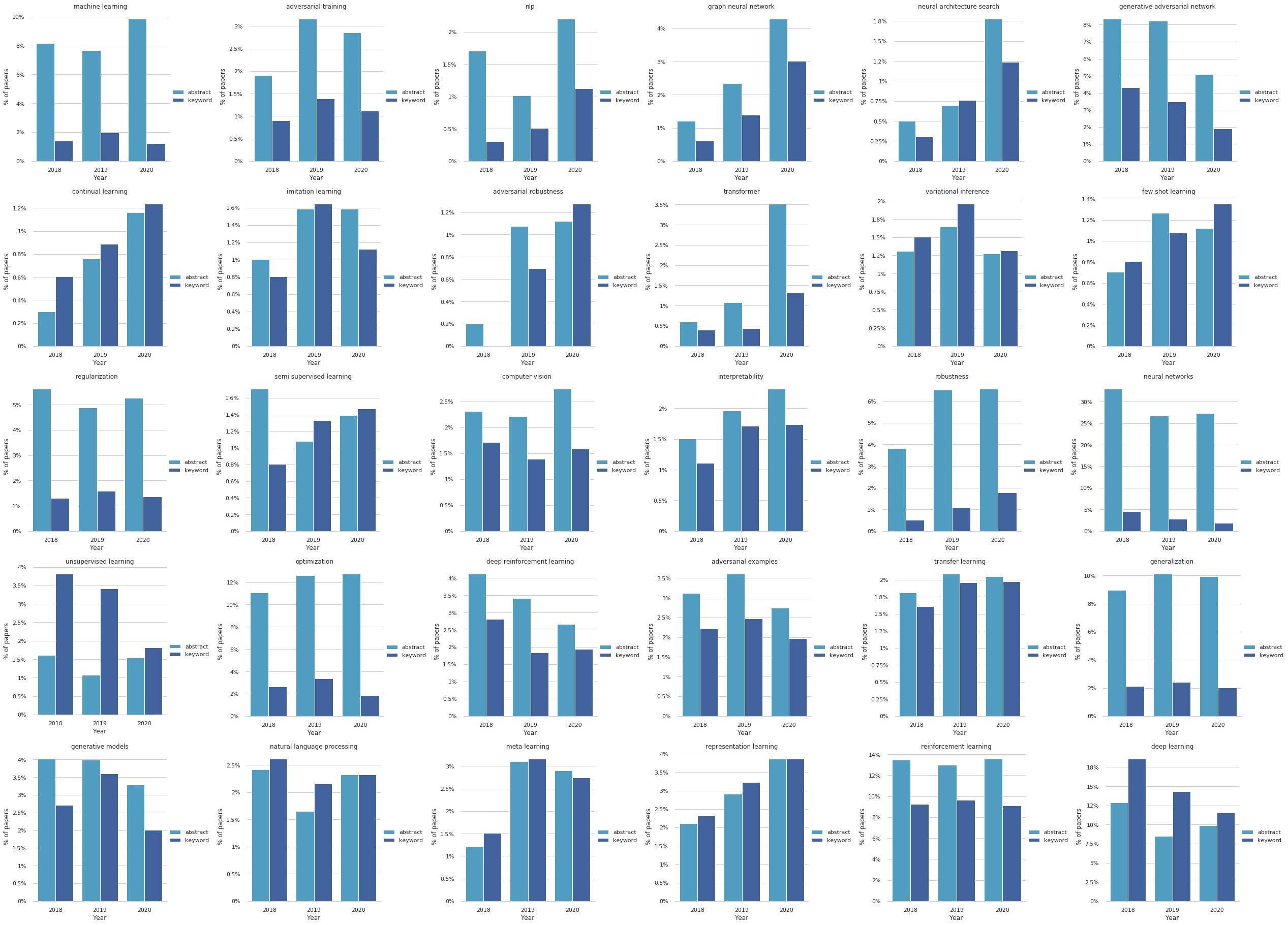
Also, the pattern-based approach not only helps spot known types of attacks but also can be useful when approaching the unknown. Harnessing the power of machine learning or reinforcement learning paradigms of supervised learning and reinforcement learning allows the neural network to learn how IT infrastructure fits into the daily work. This essentially makes it the direct opposite of a trigger-based system. Instead of spotting the signs of malicious activity, machine learning models ensure operations can detect anomalies within the system.
Policy-driven escalation and remediation
Smart alerting is a great tool for DevOps or administration specialists, though it remains only one step of their work. Any alert is a problem that needs to be fixed or at least a condition that requires supervision. In keeping IT infrastructure up and running as well, notification remains only a single step. Services lost even briefly can be very costly.
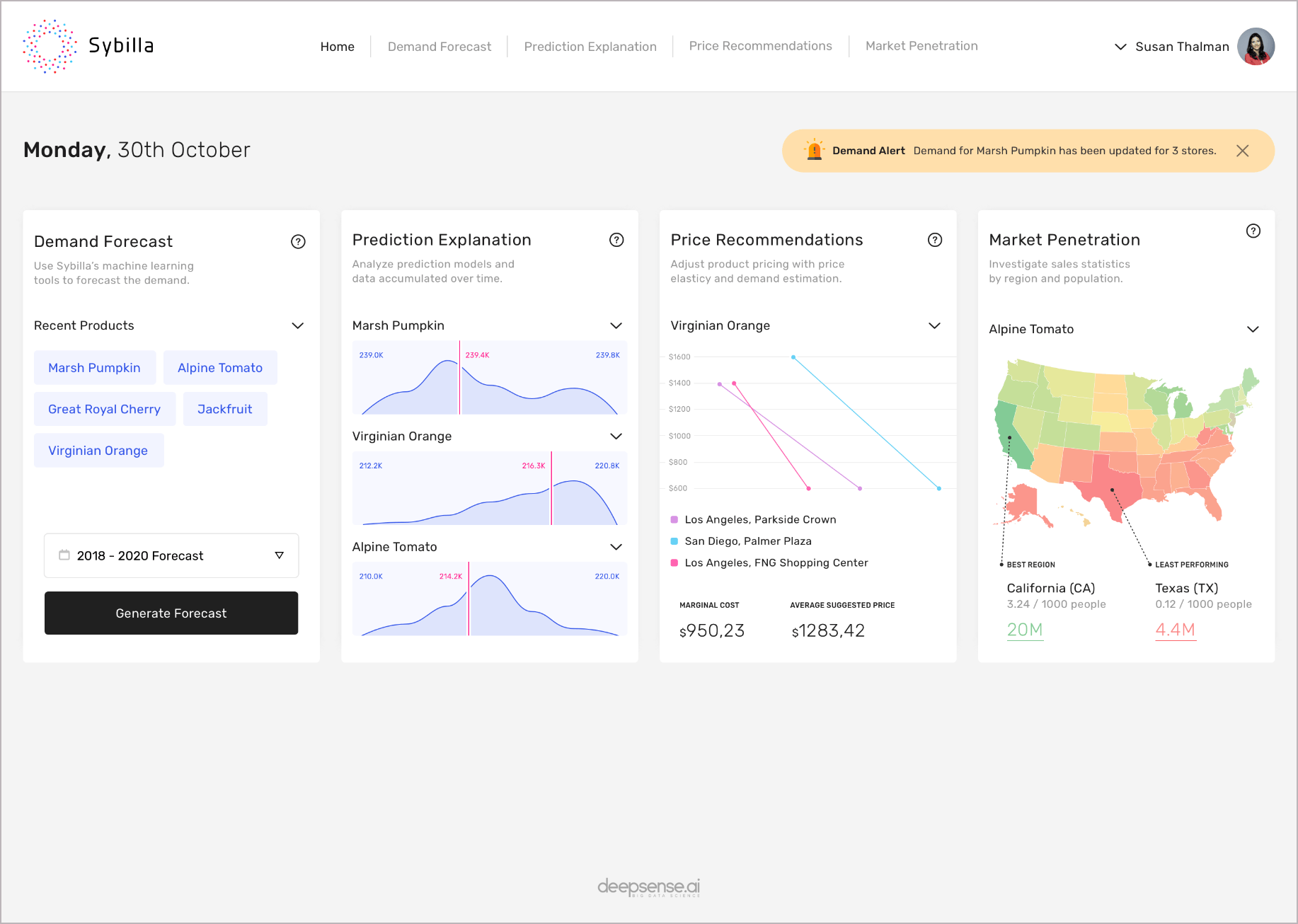
With AIOps implemented, ml-armed supervisors will not only spot the signs of a malfunction but also respond with the best policy available, according to their previous experience and information implemented in the network.
A simple example would be delivering a mirrored piece of infrastructure and redirecting the traffic while providing an alert to the supervisory team. AIOps handles this with alert escalation workflows and immediate response. Also, the AIOps infrastructure correlates the dependencies based on incoming data and responds not to a single event, but to address the group of alerts continuously. The approach saves the time usually spent grouping alerts into same-event related ones.
Key benefits of AIOps alerting
AIOps solutions have been adopted for their numerous benefits, including the following four.
- Savings – any anomalous situation in the network can result in costs skyrocketing, especially in the age of growing cloud workloads. When the company is charged for every byte of information stored or transferred, inefficiencies or instructions add up to unbearable costs, especially in the long term.
- Security – alerting delivers knowledge about anomalous situations in the system, and any anomaly can be a sign of an ongoing intrusion or malfunction that can end up shutting the system down.
- Scalability – smart alerting systems deliver more clear information about the overall state of the infrastructure. Repeating patterns in network performance are a sign to up- or downscale the entire system, be it once, with on-demand cloud solutions, or permanently by adding new components.
- Smart cloud management – delivering a real-time alert is crucial to initiating next steps; in an AIOps alert platform, these can be automated and launched contextually, as the current situation demands, not only according to predefined conditions.
Summary
Smart alerting is the foundation of next-level infrastructure management. Companies can harness the power of AI-powered solutions to optimize operations and deliver better results.
If you’d like to hear more about deepsense.ai’s AIOps platform and our approach, contact us using the form below or drop us a line at aiops@deepsense.ai.